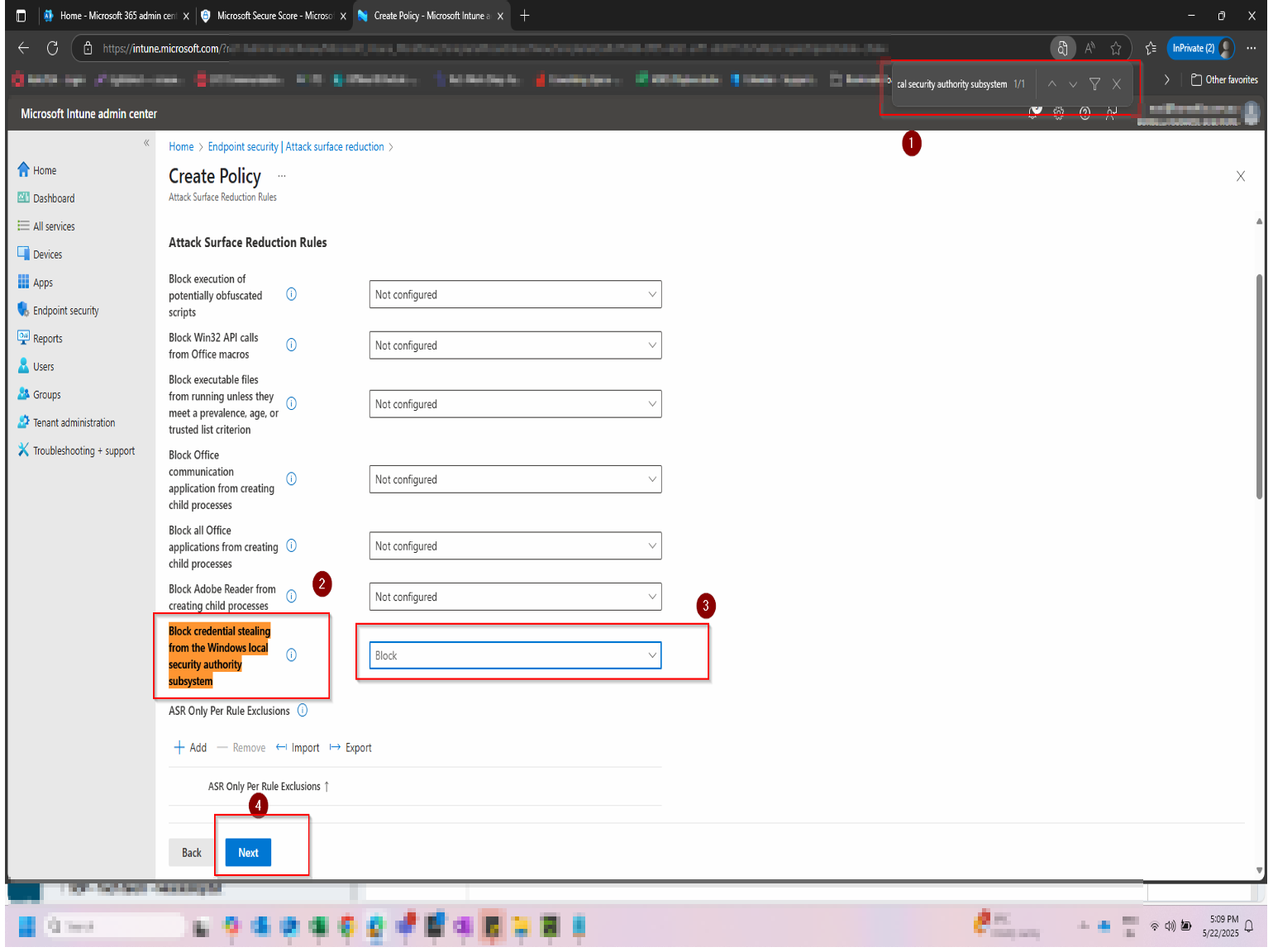
Why this setting matters
LSASS is the process Windows uses to handle authentication. It stores password hashes, Kerberos tickets, and NTLM credentials in memory — exactly what an attacker needs to move laterally across your environment or escalate privileges.
- Tools like Mimikatz and ProcDump are specifically designed to extract credentials from LSASS memory.
- Once an attacker has credentials, they can authenticate as legitimate users — making detection significantly harder.
- This ASR rule is a direct Microsoft Secure Score recommendation with meaningful score impact and low disruption risk.