Why this setting matters
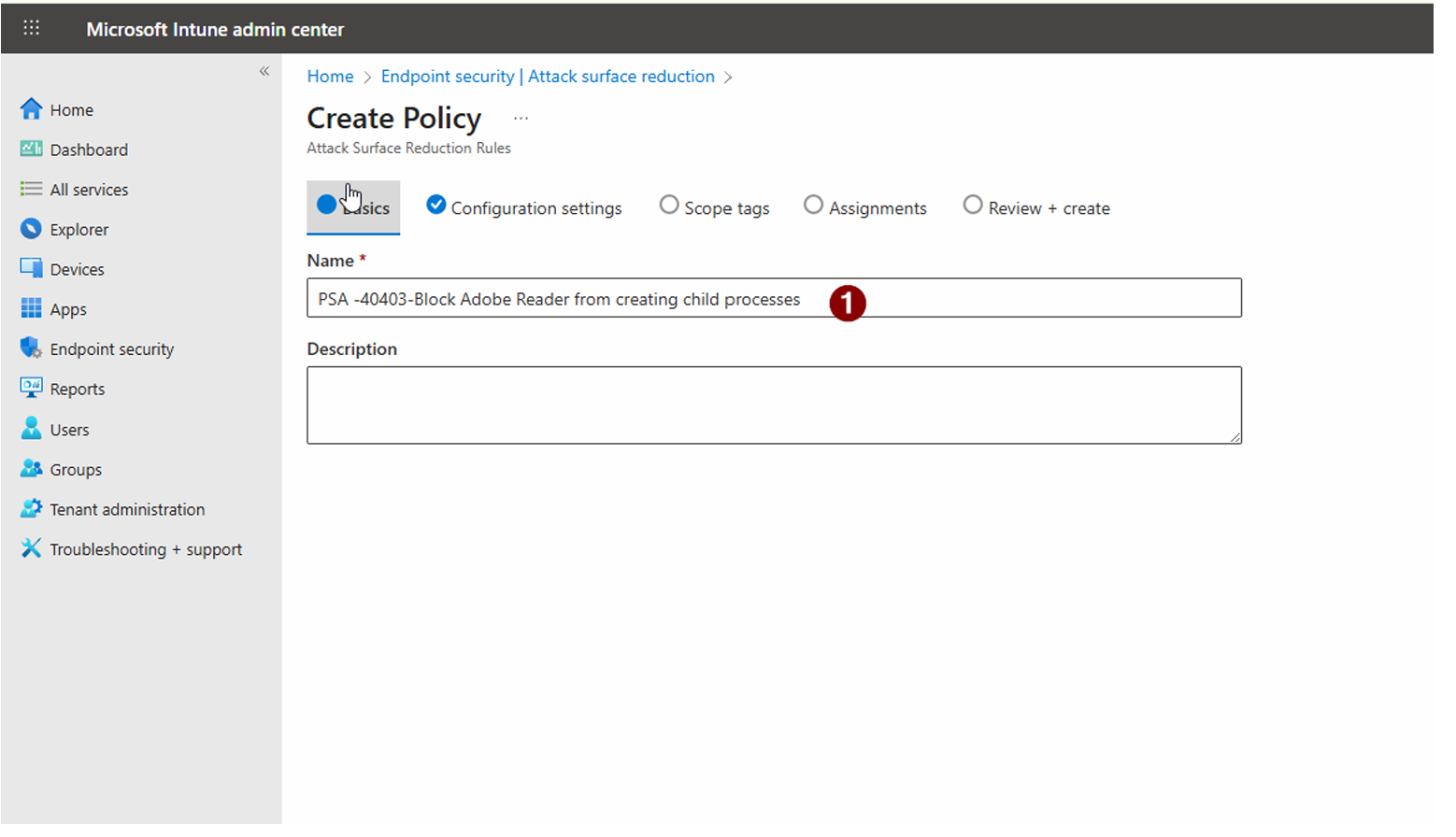
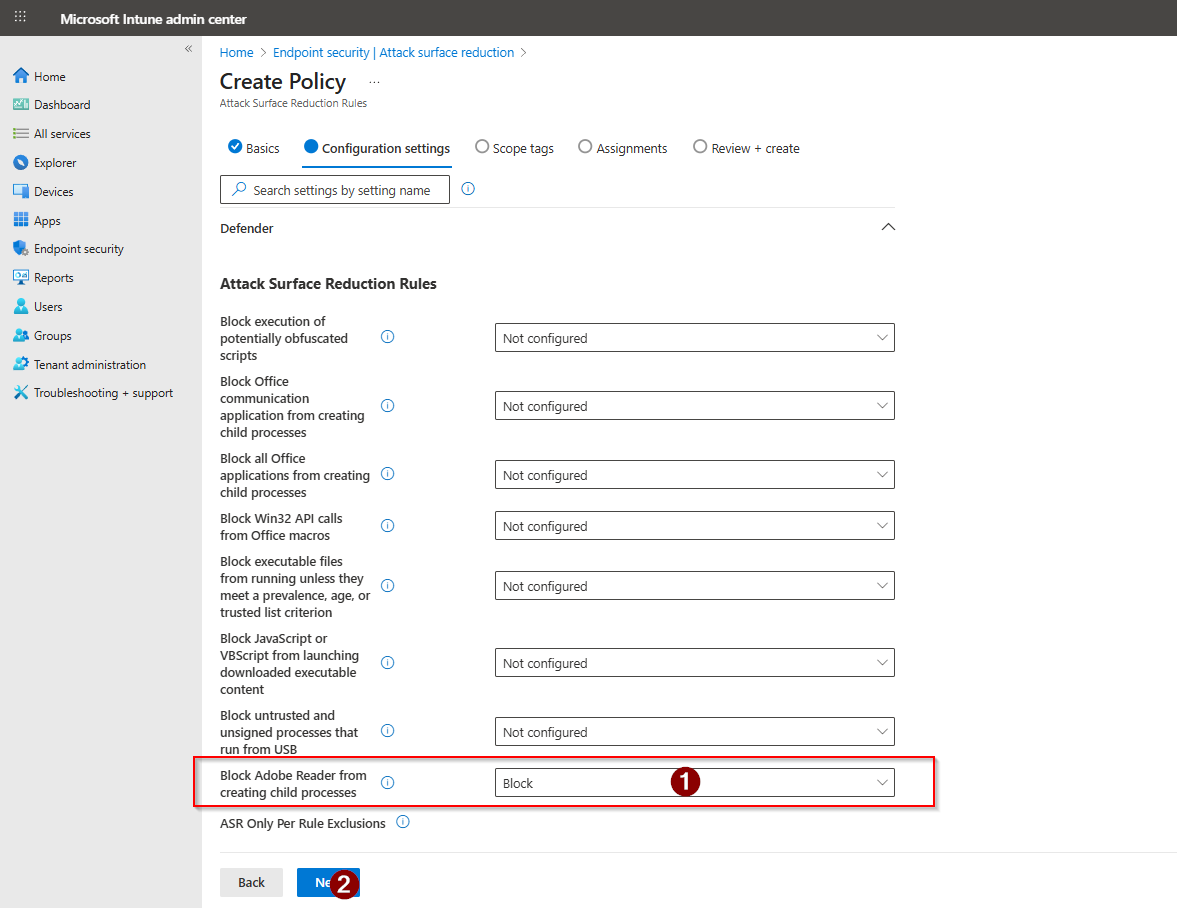
PDF files are one of the most common delivery mechanisms for malware. Adobe Reader, by default, can spawn child processes — things like command prompts, scripts, or other executables — when handling certain file types or embedded content.
- Attackers embed malicious scripts in PDFs that launch via child processes.
- Once a child process runs, it can bypass security controls and execute payloads.
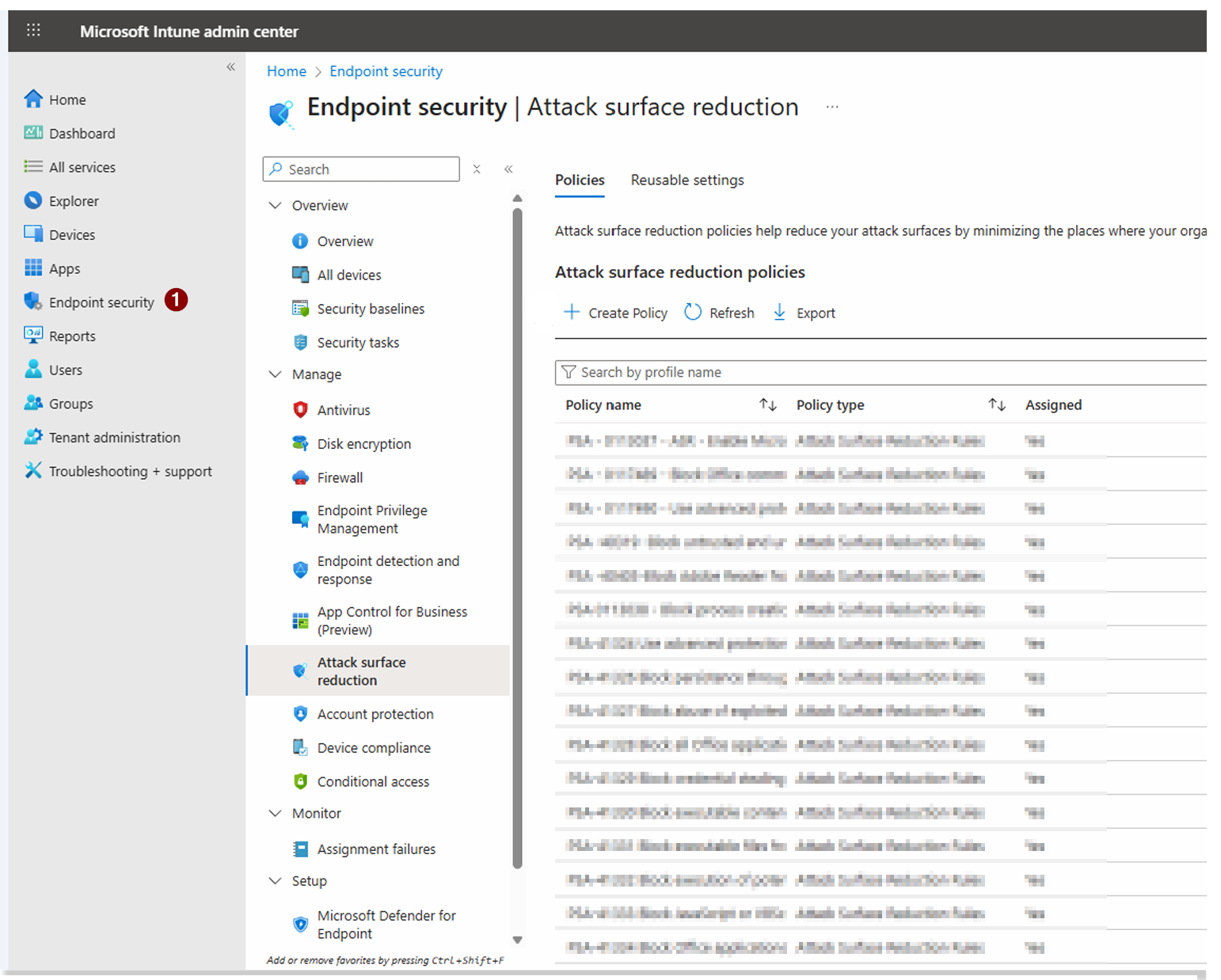
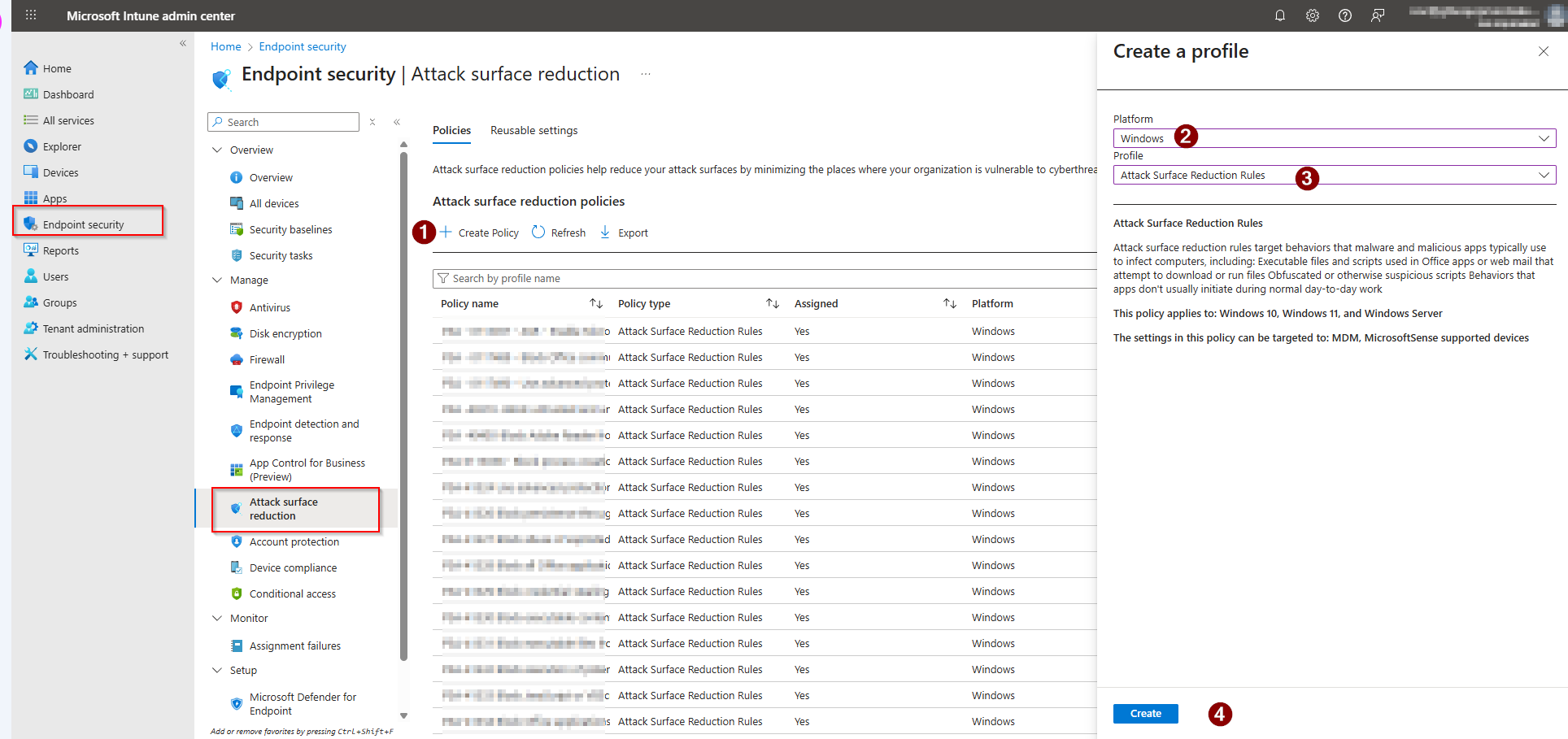
- This ASR rule is a direct Secure Score recommendation with measurable score impact.